I. Introduction
In the era of the Internet of Things (IoT), where connected devices generate vast amounts of data, the trifecta of managing IoT data—storage, analysis, and security—takes center stage. This article explores the intricacies of efficiently handling the data deluge from IoT devices, addressing storage solutions, analytical insights, and the critical aspect of ensuring robust security measures.
II. Storage Solutions for IoT Data
a. Scalable Storage Architectures
- Cloud-Based Storage: Cloud platforms offer scalable and flexible storage solutions, allowing businesses to adapt to varying data volumes from IoT devices.
- Edge Storage: Localized storage at the edge of the network enables quick access to critical data, reducing latency and bandwidth requirements.
b. Data Lifecycle Management
- Tiered Storage: Implementing tiered storage structures ensures that frequently accessed data is readily available, while less critical data is archived for cost-effective management.
- Data Compression and Optimization: Techniques like data compression reduce storage space requirements, optimizing the storage of large datasets generated by IoT devices.
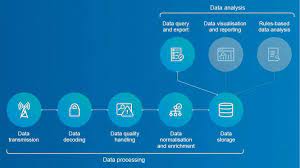
III. Analyzing IoT Data for Actionable Insights
a. Real-Time Analytics
- Edge Analytics: Processing data at the edge facilitates real-time analytics, enabling immediate responses to critical events without relying solely on centralized processing.
- Predictive Analytics: Leveraging machine learning algorithms on accumulated IoT data enables the prediction of trends and potential issues.
b. Data Integration and Interoperability
- Unified Data Platforms: Integrating diverse datasets from IoT devices into unified platforms allows for comprehensive analysis and correlation of information.
- Standardized Protocols: Adhering to standardized communication protocols ensures interoperability, fostering seamless data flow between different IoT devices.
IV. Ensuring Robust Security for IoT Data
a. End-to-End Encryption
- Secure Data Transmission: Implementing end-to-end encryption safeguards data during transmission between IoT devices, edge computing nodes, and cloud storage.
- Device Authentication: Verifying the identity of IoT devices through robust authentication protocols prevents unauthorized access and tampering.
b. Security Patching and Updates
- Firmware and Software Updates: Regular updates to firmware and software on IoT devices mitigate vulnerabilities, enhancing overall security.
- Vulnerability Assessments: Conducting routine vulnerability assessments helps identify and address potential security gaps in the IoT ecosystem.
V. Challenges and Considerations
a. Data Privacy and Compliance
- Compliance with Regulations: Adhering to data privacy regulations is crucial, especially when dealing with sensitive information from IoT devices.
- User Consent and Transparency: Ensuring user consent and transparent communication about data usage builds trust and compliance.
b. Integration with Legacy Systems
- Legacy System Compatibility: Integrating IoT data management systems with existing legacy infrastructure poses challenges that require careful planning for compatibility and coexistence.
- Scalability Concerns: As the number of IoT devices grows, scalability becomes a concern, necessitating adaptable solutions that can handle increasing data volumes.
VI. The Future Landscape of IoT Data Management
a. Advancements in Edge Computing
- Decentralized Data Processing: Edge computing advancements will further decentralize data processing, reducing reliance on centralized cloud resources.
- AI-Driven Insights: Artificial intelligence will play a more significant role in extracting meaningful insights from the vast and complex datasets generated by IoT devices.
b. Enhanced Security Measures
- Blockchain Integration: The integration of blockchain technology enhances the security and transparency of IoT data transactions, providing a decentralized and tamper-resistant ledger.
- Zero-Trust Architectures: Implementing zero-trust architectures ensures that each component of the IoT ecosystem is continuously verified, enhancing overall security.
VII. Conclusion
Effectively managing IoT data requires a comprehensive approach that addresses storage scalability, analytical insights, and robust security measures. As IoT technology continues to evolve, businesses must adapt their data management strategies to harness the full potential of connected devices while safeguarding against potential risks. The future holds exciting possibilities as advancements in edge computing, artificial intelligence, and enhanced security measures reshape the landscape of IoT data management.
FAQs
- Q: Why is edge storage important for IoT data management?
- A: Edge storage reduces latency and enhances real-time access to critical data generated by IoT devices, improving overall responsiveness.
- Q: How can businesses ensure the security of IoT data during transmission?
- A: Implementing end-to-end encryption ensures secure data transmission between IoT devices, edge computing nodes, and cloud storage.
- Q: What role does artificial intelligence play in IoT data management?
- A: Artificial intelligence enables predictive analytics, extracting meaningful insights from IoT data and predicting trends and potential issues.
- Q: How can IoT data management systems address scalability concerns?
- A: Adaptable solutions that can handle increasing data volumes and advancements in edge computing will address scalability concerns in IoT data management systems.
- Q: What are the future trends in IoT data management?
- A: Advancements in edge computing, integration of blockchain technology, and the adoption of zero-trust architectures are future trends shaping IoT data management for enhanced security and insights.